Another good online tool to check if your e-mail has been compromised is the Identity Leak Checker. 02 Firefox Monitor by Mozilla Have your accounts been leaked or stolen in a data breach.
Click on the gear icon and click Mail.
How to check if email is compromised. Another good online tool to check if your e-mail has been compromised is the Identity Leak Checker. This tool was created by German-based Hasso-Plattner Institute HPI and the exciting feature about Identity Leak Checker is that it does not only check the internet for compromised e-mails but also personal identity theft. All you have to do is access the tool via HPIs website input your e-mail.
Breach Cheker is a free tool which helps you find out if your email got compromised in a data breach. We rely on a database of historical and recent breaches from hundreds of sites. This helps you assess your risk level of a potential hack and secure your account.
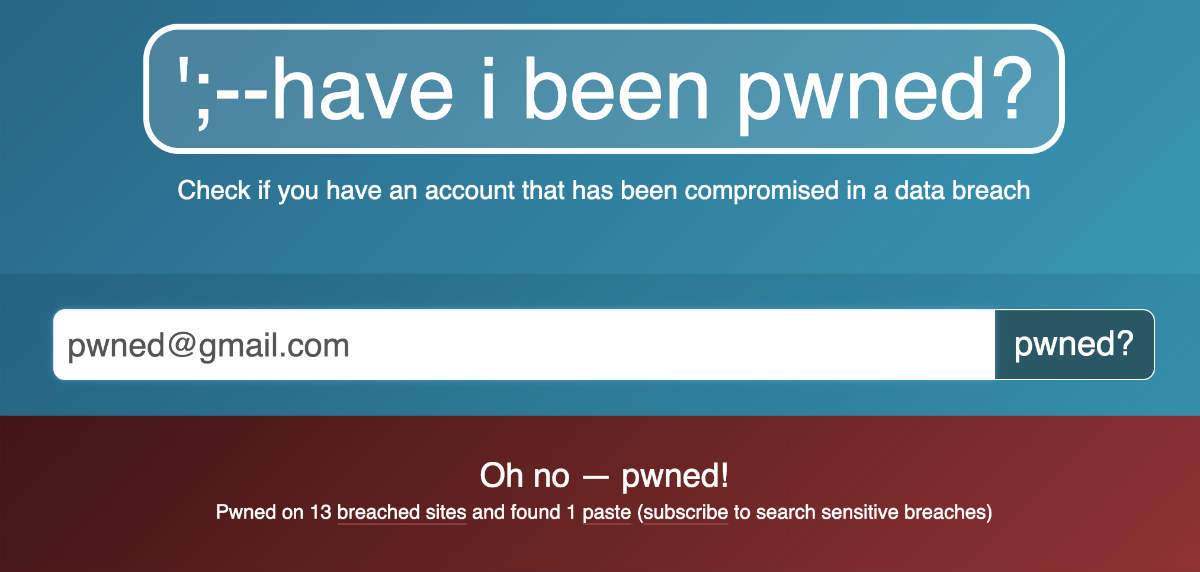
To check if your password may have been exposed in a previous data breach go to the sites homepage and enter your email address. The search tool will. If your email address has been compromised because of multiple breaches like the one below you can look through the lists and find out which ones are the most dangerous.
If you use the same email address across multiple websites make sure to have a different password for each. In short it is a reverse search engine that will check your email or password against a huge list of stolen data from various sources. To know if any of your account was compromised just search for your own email address or password.
02 Firefox Monitor by Mozilla Have your accounts been leaked or stolen in a data breach. If your email account has been compromised you can take some simple steps to put things right. Create a new email address The best thing to do is close the compromised account down and open a new one.
Make sure you use a strong password combining. Find out with Avast Hack Check. Just put one of your email addresses in the field below and well see if any accounts linked to it have been compromised.
Receive 24-hour automatic email alerts anytime your password leaks. Find if your Linkedin Facebook Twitter. Just type in your email address and the site will search the breached data and showcase any red flags.
You can also search for more sensitive breaches but. Users can check if their email addresses or phone numbers. A data breach occurs when cybercriminals hack into organizations databases and steal sensitive information.
The data which is exposed to the public can include passwords account numbers correspondence names home addresses Social Security numbers and more. Enter an email address below and click for immediate results. But you shouldnt use them to check your email inbox as they might have a Keylogger or malware.
And even if theyre not you should still log out as soon as you finish so that no one after you can see your messages. There are other ways that hackers can use to hack your e-mail but these are by far the most common and now that you learned about these lets take a look next at. You can check out services such as Have I Been Pwned by entering your email address in the corresponding field and the feature will tell you if youve been compromised.
If your mail is indeed listed you will be shown the websites to which your email may have leaked. Click on the gear icon and click Mail. Click Inbox and sweep rules and review the rules.
Disable or delete suspicious rules. Step 4 Unblock the user from sending mail. If the suspected compromised mailbox was used illicitly to send spam email it is likely that the mailbox has been blocked from sending mail.
Ideally when you enter the 62 code you should see nothing. If your phone is forwarding to another number it will display after you enter the 62 code. You should see the 10 digit phone number where your calls and messages are being forwarded.
You can also check for. If you notice something get in touch with your bank. If everything looks fine check back in a week or two and verify.
Then do the same thing a week or two after that. Sometimes hackers will wait a while before they try to sneak in a purchase or two. Check for any suspicious activity.
If you find activity that didnt come from you select No it wasnt me. Then follow the steps on the screen to help secure your account. If you did the activity select Yes.
If you still believe someone else is using your account find out if your account has been hacked.